Runtime oversight for autonomous agents — YAML identity manifests with trust levels 1-5, 3-tier tool classification, append-only audit logging, constitutional contracts with monotonically decreasing privileges, memory governance, and trust-mediated delegation with 6 sequential gates.
Autonomous AI agents can read files, write code, execute commands, access external services, and delegate to other agents. Without runtime governance, there's no enforcement boundary between what an agent can do and what it should do. "Trust but verify" doesn't work when agents operate faster than humans can review.
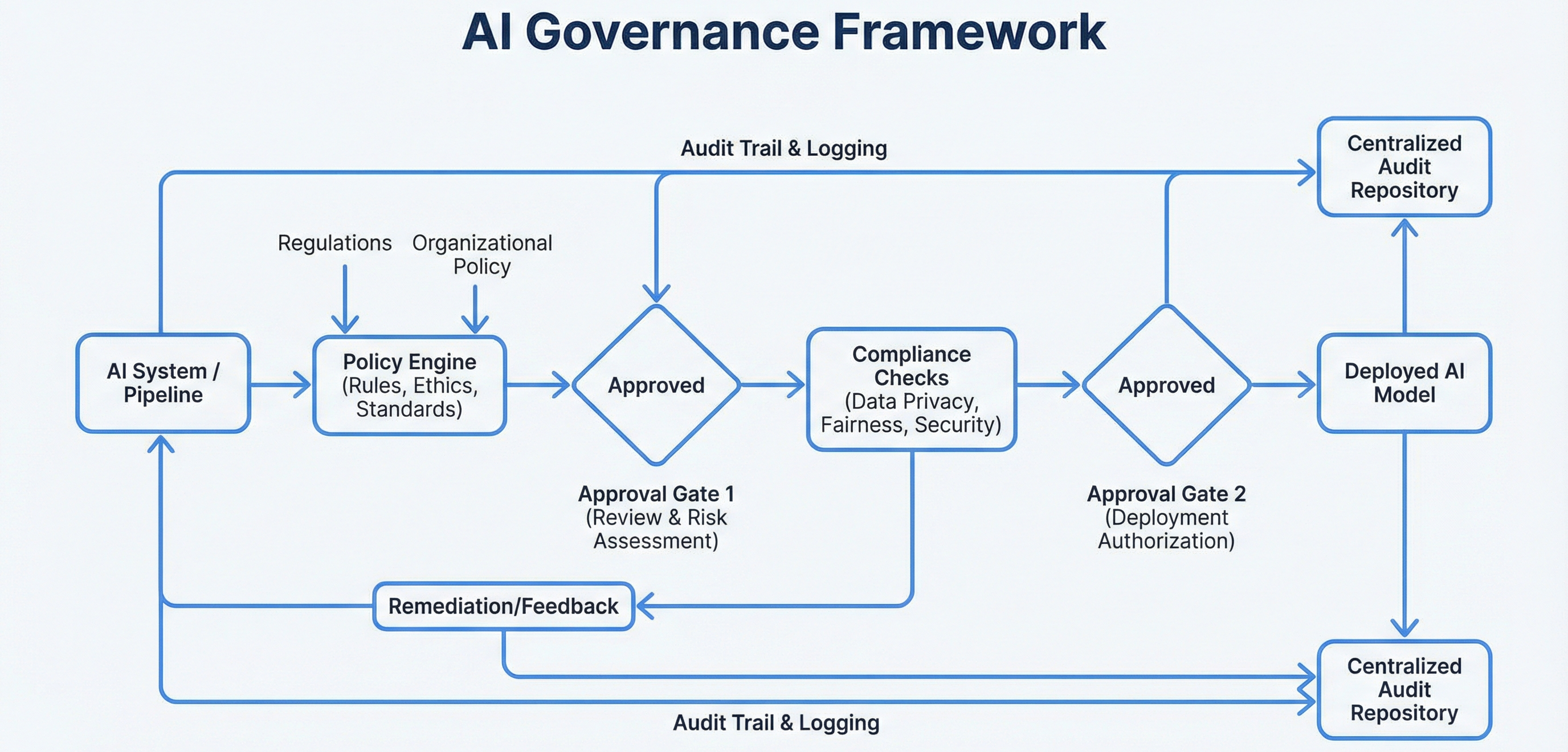
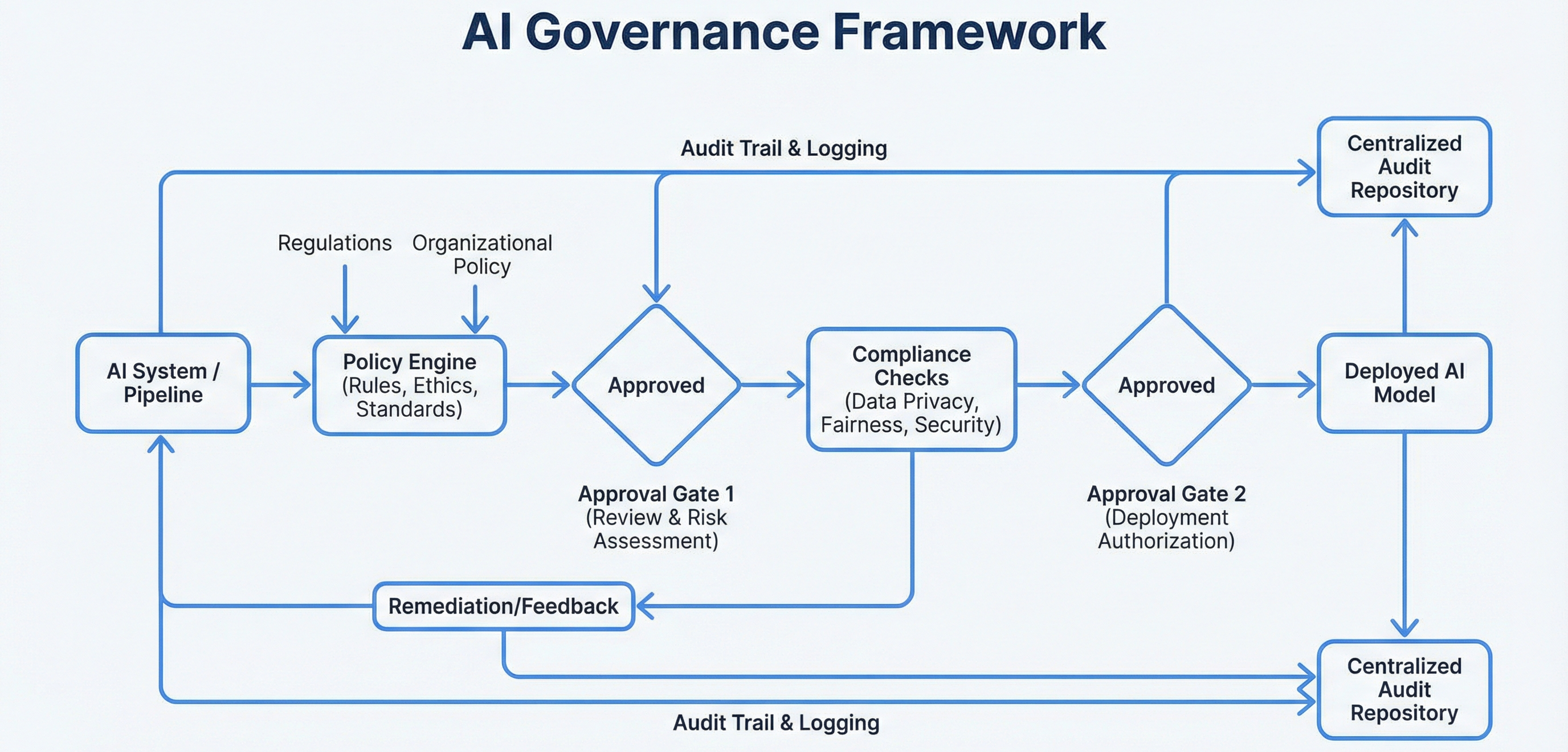
The governance framework provides enforcement at the speed of execution — policy evaluated in milliseconds, not minutes. It's implemented in two layers: the governance plugin (Python, SQLite audit bus, policy engine, trust broker) and 7 governance MCP tools in the memory system (constitutional contracts, compliance dashboards, guardrail proofs, data sovereignty).
Who is this agent? Trust 1-5, data classification, permitted tools/delegations
3-tier tool classification × conductor tier matrix
SQLite WAL, 19+ event types, sync/async emission
Content classification, ceiling enforcement, provenance
6-gate delegation mediation, delegation tokens
7 MCP tools for contracts, monitoring, proofs, sovereignty
SessionStart → Load manifests, init audit session, register agents
PreToolUse → Policy engine evaluates tool call against manifest + constitutional observer checks drift
PostToolUse → Audit bus logs outcome, memory governor checks content classification
Stop → Deregister agents, flush constitutional assessments, archive sessionagent_id: code-reviewer
trust_level: 3 # 1 (minimal) to 5 (full)
data_classification: internal # public | internal | confidential | restricted
permitted_tools: [Read, Glob, Grep, Bash]
permitted_delegations: ["qa-*", "builder"] # fnmatch patterns
max_autonomy_depth: 2
max_delegation_count: 5
human_required: false4-tier resolution: Static YAML + parent → ceiling enforcement (intersection); static only → authoritative; parent only → derived restrictive (trust-1); neither → default restrictive (trust=1, no tools, human_required=true). SHA-256 hashed for tamper evidence.
Most daily work: zero approval prompts, <200ms total overhead. Human approval only when elevated tool + MAJOR tier.
| Tier | Tools | Overhead |
|---|---|---|
| Exempt | Read, Glob, Grep, TaskList, TaskGet, AskUserQuestion | Zero (async log only) |
| Standard | Edit, Write, Task, Bash, WebFetch, WebSearch | ~50ms auto-allow + audit |
| Elevated | memory_store, memory_forget, NotebookEdit, all MCP tools | ~100ms or human gate at MAJOR |
| Conductor Tier | Exempt | Standard | Elevated |
|---|---|---|---|
| TRIVIAL | Allow | Allow | Allow |
| MINOR | Allow | Allow | Allow |
| STANDARD | Allow | Allow (audited) | Allow (audited) |
| MAJOR | Allow | Allow (audited) | Human Gate |
Beyond the governance plugin's policy engine, 7 MCP tools in the memory system add runtime constitutional governance:
The constitutional observer hook (PreToolUse, <2s, no LLM) checks every tool call for drift and feeds assessments to the compliance layer.
SQLite WAL, 19+ event types, hybrid sync/async emission. Sync for denials/threats (with alerting), async for allows (bounded queue, 256 max, daemon worker). JSON-lines buffer fallback. 90-day retention with JSONL archival.
| # | Gate | Check |
|---|---|---|
| 1 | Breadth | max_delegation_count not exceeded? |
| 2 | Depth | max_autonomy_depth > 0? |
| 3 | Classification | Target classification ≤ source? |
| 4 | Trust | Target trust ≤ source? (no escalation) |
| 5 | Targets | fnmatch pattern match on permitted_delegations? |
| 6 | Registration | Manifest registered in TTL-3600s session registry |
Query events, export JSONL
Health dashboard + metrics
Approve/deny confidential writes
Build an agent governance framework for Claude Code:
1. IDENTITY MANIFESTS (YAML): agent_id, trust_level 1-5,
data_classification, permitted_tools/delegations, autonomy depth/count,
SHA-256 hashing, 4-tier resolution with parent ceiling
2. POLICY ENGINE: 3-tier tool classification (exempt/standard/elevated)
× conductor tier matrix. Human gate only at MAJOR+elevated.
Unknown tools → elevated. Typical overhead: <200ms, zero prompts.
3. AUDIT BUS: SQLite WAL, 19+ event types, sync for denials,
async for allows (bounded queue 256), JSON-lines buffer fallback,
90-day retention + JSONL archival
4. CONSTITUTIONAL LAYER (7 MCP tools):
- constitutional_contract: monotonically decreasing delegation privileges
- constitutional_monitor: real-time drift detection
- guardrail_proof: Ed25519 + Merkle attestation
- data_sovereignty: jurisdiction tagging, GDPR cascading delete
- governance_report/gap_analysis: ISO 42001 evidence
- compliance_dashboard: ISO 42001 + EU AI Act + OWASP scoring
Plus constitutional_observer hook (<2s PreToolUse, no LLM)
5. MEMORY GOVERNOR: regex content classification
(restricted=block, confidential=queue), ceiling enforcement,
provenance tagging (agent_id + manifest_hash)
6. TRUST BROKER: 6 sequential gates (breadth, depth, classification,
trust, targets, registration), 24-char hex delegation tokens,
ManifestRegistry with file locking + TTL purge
7. COMMANDS: /governance-audit, /governance-status, /governance-review
Build as Claude Code plugin (Python) + 7 MCP tools in memory server.The governance plugin (Python, SQLite) handles runtime policy enforcement. The memory system's 7 MCP tools handle constitutional contracts, compliance, and cryptographic proofs. Neither alone is sufficient — together they cover both enforcement and evidence.
Exempt tools add zero overhead. Standard tools add imperceptible ~50ms. Only elevated tools trigger full evaluation. This keeps governance invisible for routine work while maintaining scrutiny where it matters.
Real-time drift detection on every tool call (<2s, no LLM) catches problems as they happen. Buffered flags flush to vector storage at session end for trend analysis. The compliance dashboard reads these for scoring.
Child agents inherit the intersection of their permissions and parent permissions. A trust-3 parent cannot create a trust-5 child. This is mathematically guaranteed to prevent privilege escalation through delegation chains.
Governance operates as a plugin using SessionStart (manifest loading), PreToolUse (policy enforcement), PostToolUse (audit logging). The two-layer hook system ensures reliable execution.
Conductor's tier classification feeds the policy engine's tier matrix. NHI lifecycle events emit to the audit bus. The state schema's governance block links manifests to workflows.
7 governance MCP tools operate within the memory server. Memory governor controls what enters vector storage. Constitutional assessments stored in dedicated Qdrant collection.
Context pressure events become CONTEXT_PRESSURE audit entries. Constitutional observer flags decisions made under context pressure for governance review.